If you’ve ever encountered Ransomware, you’ll know how devastating it can be to be locked out of all your files. It’s no surprise, then, that ransomware has been one of the major topics of internet security discussion over the past 18 months. Kaspersky labs reported that during 2015, ransomware was detected on 753,684 computers of unique individuals, with 179,202 computers being targetted by encryption ransomware, and Statista published a report stating that 51% of internet users are concerned or very concerned about the threat of ransomware.
One of the major factors contributing to the growing popularity of ransomware among cyber-criminals is that it’s relatively easy to set up. In fact, it’s been so successful that it’s now commonly sold as ‘ransomware as a service‘ – you’ll even find some authors adopting an affiliate model to increase their sales. It seems like ransomware is here to stay.
There’s plenty to learn about ransomware, and not enough space to explain it all here. However, if you want to find out more about what you’re up against, BestVPN and Fossbytes both offer excellent introductory guides.
Alternatively, read on to find out exactly what you can do to keep your files safe here and now.
Minimise Risk of Ransomware Infection
Use antivirus software and keep it up-to-date.
Avast and AVG are both excellent free antivirus programs that will help you avoid being infected in the first place.
Keep your operating system patched.
Viruses can exploit weaknesses in an OS’s security. Make sure yours isn’t unnecessarily vulnerable.
Don’t click that link!
There are certain online habits that make your computer more likely to become infected with malware. One of the quickest, most surefire ways is to click links without first questioning whether they’re from a trustworthy source. These links may be in unsolicited emails, popups, and websites, and can often be found lurking on the less reputable torrent sites too. In fact, several major sites have been found to be spreading ransomware through their ad-network.
Be careful what you download.
How much do you want that keygen for your new pirate copy of the latest image editing suite? Enough to risk losing all your documents? Don’t say we didn’t warn you.
Always Be Prepared
If the above fails, and you find yourself being held to ransom by online thieves, you’ll be glad you followed the advice that follows. The following steps outline a backup and restoration process to get your computer back to how it was before the attack.
Create a bootable Windows drive.
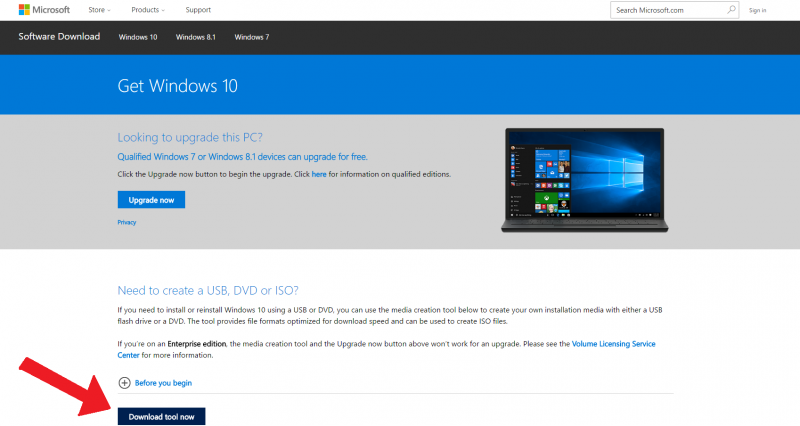
You can make set up a USB drive that will allow you to install your original copy of Windows onto a fresh hard drive. It’s pretty simple, just follow these instructions from Microsoft.
Keep your data secure both locally and online
There are many different ways to keep your data backed up, but online and using a local storage device are two of the best if you’re looking after personal, rather than company, files.
External hard drives
These useful devices are continually increasing in storage capacity and decreasing in price – with most brands now offering 1TB for less than $50, or 2TB for under $100. You’ll need to update them manually, but they’re the perfect place to store files that you don’t plan to update regularly. Check here to find out what’s available on Amazon.
NAS
Network attached storage (NAS) devices are perfect if you want to backup from multiple devices at home or in the office. QNAP and Synology are two of the best manufacturers when it comes to commercial NAS devices (link), or you can try your hand at making your own (link).
Online backups
This option protects you in case the files on your external hard-drive get infected, or if your drive gets destroyed by something as simple as a spilled drink. One of the major advantages of online backup services like Backblaze and Carbonite is that they will keep continuous, automatic backups – so that whenever you make a change to a backed up file, it’ll automatically be applied to the copy that’s saved in the Cloud.
This means that the most recent version of your files will always be saved, without you having to worry about manually uploading your changes. Choose a backup provider that offers versioning, and you’ll always have a backup of your files and any changes you make to them. Many of these services offer great guides for setting up versioning, and others, such as Crashplan, can even help you with what to do if you get ransomware.
If you want to make 100% sure that your files will be secure no matter what, it’s well worth taking the tried and tested 3-2-1 backup approach, and saving your data in several locations – both in and out of the Cloud.
Backup your personal files
Use file versioning
One of the biggest questions when it comes to overcoming ransomware is ‘can ransomware affect backed up files?’

Unfortunately, it is possible, as the downside of continuously updating the backed up copies of your files is that you might end up storing ransomware too. Fortunately, there is a solution.
When it comes to online backups, file versioning is the process by which your backup provider doesn’t just hang on to the current iteration of your files – it also lets you restore previous drafts of them that have since been saved over. This means that, if your documents have been stored after being infected by ransomware, you’ll be able to go back and retrieve a copy that was saved before you contracted the virus. You may lose a couple of changes, but you certainly won’t have to worry about paying up to get ahold of your files.
You can also apply versioning to local backups using Microsoft File History by running a complete backup of your personal files and setting up versioning. When the hard drive isn’t connected to your computer, the versions stay in a temporary folder, so just be sure to connect every few days and you’ll have both old and new copies of your documents safely backed up. Again using Microsoft File History, do a complete backup of your personal files and set up versioning so that every time you make a change to a document, it will save the changes to your backup. When the hard drive isn’t connected to your computer, the versions stay in a temporary folder, so just be sure to connect every few days and you’ll have all your recent documents and edits safely backed up.
Ransomware Removal
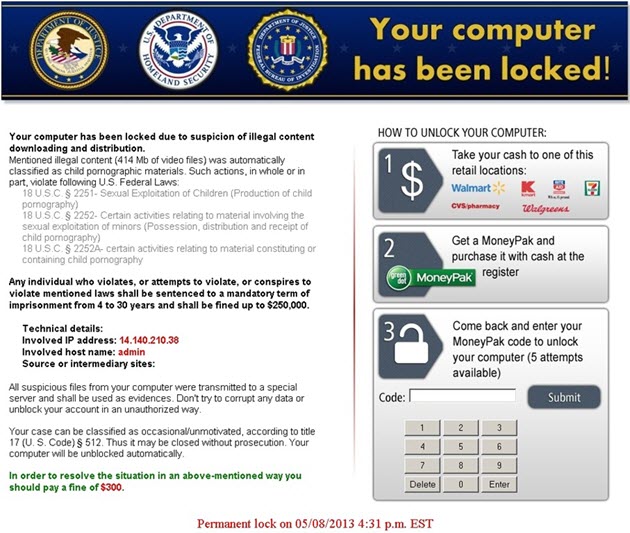
Discovered ransomware on your computer? Never fear – even if you don’t pay out, you can still return it to its original state.
First and foremost, you’ll need to disconnect from the internet as soon as you discover the infection. If you’re lucky, you may have been infected by a version that’s already been patched, such as CryptXXX or CoinVault. Use another computer to search for possible fixes for your version. If you can’t find a solution, you could try taking your laptop to a computer shop to ask for help, but if you’ve been infected with a file-encrypting ransomware, then it’s unlikely they’ll be able to help.
This is when it’s time to start congratulating yourself for keeping an up-to-date version of your computer. Follow these instructions restore your computer to its clean state.
Buy a new internal hard-drive.
This is a bit annoying, but it’s the safest way to make sure you get rid of the virus. Check here for what Amazon offers. If you’re replacing anyway, why not upgrade to an SSD drive for increased speed.
Replace your infected hard drive.
The exact process will depend on the manufacturer and model of your computer, but it’s usually a fairly painless process. A Google search for “how to replace hard drive computer, model” should bring up exactly what you need.
Install the clean copy of Windows from your bootable USB drive.
I recommend keeping all the settings (such as name) the same on your new OS, to avoid any problems with file paths not being recognized when you restore.
Download a virus scanner such as Avast or AVG

and do a scan of your external hard drive to make sure the infection didn’t spread. If all is well, you can go ahead and restore your most recent system image and file versions.
If there are any issues with your external hard drive, head over to Crashplan and start the restoration process
Conclusion
There’s really no way of knowing how long the internet will be plagued by ransomware, but if BitDefender’s predictions are to be believed, things are only going to get worse. If you follow the steps detailed above you will have a robust ransomware avoidance and removal strategy that will keep all your files protected even in the event of encryption.
“But all this new hardware and online backup seems expensive, wouldn’t it be easier to just pay the ransom?”
Well, no. For one, there’s the principle. Why should you bow down to cyber criminals? Secondly, there’s the fact that by paying them, you become part of the system that funds them, which keeps the business alive. Finally, remember you are dealing with dishonest people. How do you know that they will even give you your files back if you pay? This hospital found that out the hard way.
Drop a comment below if you have any thoughts or questions about what I’ve described above.


![Ransomware – Protect Windows Files [Foolproof method]](/wp-content/themes/featherlight/timthumb.php?w=826&h=418&zc=1&src=https://www.bestbackups.com/wp-content/uploads/2016/05/ransomware-01.png)


